In the digital age, protecting your data is more crucial than ever. With the rise of remote working and the increasing use of mobile devices, endpoint data protection has become a vital aspect of cybersecurity. This article will guide you through the ins and outs of endpoint data protection, why you need it, and how to implement it effectively.
What is Endpoint Data Protection?
Endpoint data protection is a security strategy that focuses on securing data on endpoint devices like desktops, laptops, and mobile devices. It’s all about safeguarding your data, whether it’s stored on your device or in transit.
Importance of Data Protection in the Era of Remote Working
With the shift to remote working, endpoint data protection has become even more critical. Your home office is now an extension of your company’s network, making it a potential entry point for cyber threats.
Understanding Endpoint Data and Endpoint Security
What is Endpoint Data?
Endpoint data refers to any data that is processed, stored, or transmitted on an endpoint device. This could be anything from sensitive company documents on your laptop to personal information on your smartphone.
The Role of Endpoint Security in Protecting Data
A small business endpoint security solution is all about protecting these devices from cyber threats. It involves using security software, often referred to as an Endpoint Protection Platform (EPP), to detect and block threats before they can cause harm.
Endpoint Protection Platforms (EPP) and Their Importance
Endpoint Protection Platforms (EPP) are comprehensive security solutions that provide a range of protections for endpoint devices. They are a crucial component of any endpoint data protection strategy.
Endpoint Devices: Desktops, Laptops, and Mobile Devices
Endpoint devices are the gateways to your network. They include any device that connects to your network, such as desktops, laptops, and increasingly, mobile devices.
The Need for an Endpoint Protection Console
The Role of an Endpoint Data Protection Console
A console provides a centralized location for managing and monitoring your endpoint security. It allows you to keep track of all your devices, update security policies, and respond to threats quickly.
How Endpoint Protection Platforms (EPP) Enhance Security and Compliance
Endpoint Protection Platforms (EPP) play a crucial role in maintaining security and compliance. They provide a range of protections, including antivirus, intrusion detection capabilities, and firewalls. Thus, helping you meet compliance requirements and keep your data safe.
Risks of Neglecting Protecting Data
Data Loss and the Importance of Endpoint Backup
Without proper endpoint data protection, you risk losing your data. Endpoint backup solutions can help prevent data loss by regularly backing up your data, ensuring it can be recovered in the event of a disaster.
The Threat to Sensitive Data and the Role of Data Loss Prevention (DLP)
Sensitive data, such as customer information or intellectual property, is a prime target for cybercriminals. Data Loss Prevention (DLP) tools can help protect this data by detecting and preventing unauthorized data transfers.
The Impact on Enterprise Networks and Data Centers
A single compromised endpoint can put your entire network at risk. It’s crucial to protect your endpoints to prevent threats from spreading to your data centers and other critical infrastructure.
Implementing Endpoint Data Protection
Choosing the Right Endpoint Protection Platform (EPP)
Choosing the right Endpoint Protection Platform (EPP) is a crucial step in your endpoint data protection strategy. An EPP is a comprehensive security solution that safeguards endpoint devices from threats and attacks. Here are some key features to consider when selecting an EPP for optimal data protection.
Products like CrowdStrike Falcon and Microsoft Defender for Endpoint are popular choices that offer these features. Remember, the best EPP for your organization will depend on your specific needs and environment. It’s important to evaluate multiple solutions and choose the one that best fits your requirements.
Threat Detection and Response
The EPP should have robust threat detection capabilities, including the ability to identify and respond to both known and unknown threats. This includes traditional threats like viruses and malware, as well as more advanced threats like zero-day exploits and ransomware. Tools like real-time threat intelligence and behavioral analysis can help in this regard.
Data Loss Prevention
Data Loss Prevention (DLP) features are essential for preventing sensitive data from leaving your network. This includes tools for detecting and blocking unauthorized data transfers, as well as features for classifying and protecting sensitive data.
Device Control
The EPP should provide control over the use of removable devices and peripheral ports, which can be potential vectors for data loss or malware infection. This includes the ability to block or restrict the use of USB drives, printers, and other devices.
Encryption
Encryption is a crucial tool for protecting data, especially data that is stored on mobile devices or transmitted over unsecured networks. The EPP should provide strong encryption for data at rest and in transit.
Integration with Other Security Tools
The EPP should integrate well with other security tools in your environment. This can help provide a more comprehensive view of your security posture and allow for more effective response to threats.
Ease of Management
The EPP should provide a centralized management console that allows for easy configuration and monitoring of security policies across all endpoint devices. It should also provide detailed reporting and analytics to help track and improve your security posture.
Performance
The EPP should provide strong security without significantly impacting system performance. Look for solutions that are lightweight and efficient, and that won’t slow down your devices or network.
The Role of the Operating System in Endpoint Security
Your operating system plays a crucial role in endpoint security. It’s important to keep it updated with the latest security patches and to use security features built into the OS, like Windows Defender on Windows or Gatekeeper on macOS.
Cloud-Based Solutions for Data Protection
Cloud-based solutions, like Sophos Endpoint Protection, offer a flexible and scalable approach to endpoint data protection. They allow you to manage and protect your devices from anywhere, making them a good fit for remote work environments.
Monitoring and Managing Data for Optimal Protection
Access Control and Its Importance in Data Security
Access control is a crucial part of data security. It involves ensuring that only authorized individuals have access to your data. Tools like Cisco Identity Services Engine can help manage access control effectively.
Best Practices for Managing Data on Endpoint Devices
Managing data on endpoint devices involves following best practices like regularly updating software, using strong passwords, and encrypting sensitive data.
Conclusion: The Future of Endpoint Data Protection
The Increasing Relevance of Endpoint Data Protection in a Remote Working World
As remote work becomes more common, endpoint data protection will only become more important. It’s crucial to stay informed and proactive in protecting your data.
Final Thoughts on the Importance of Security and Compliance in Endpoint Data Protection
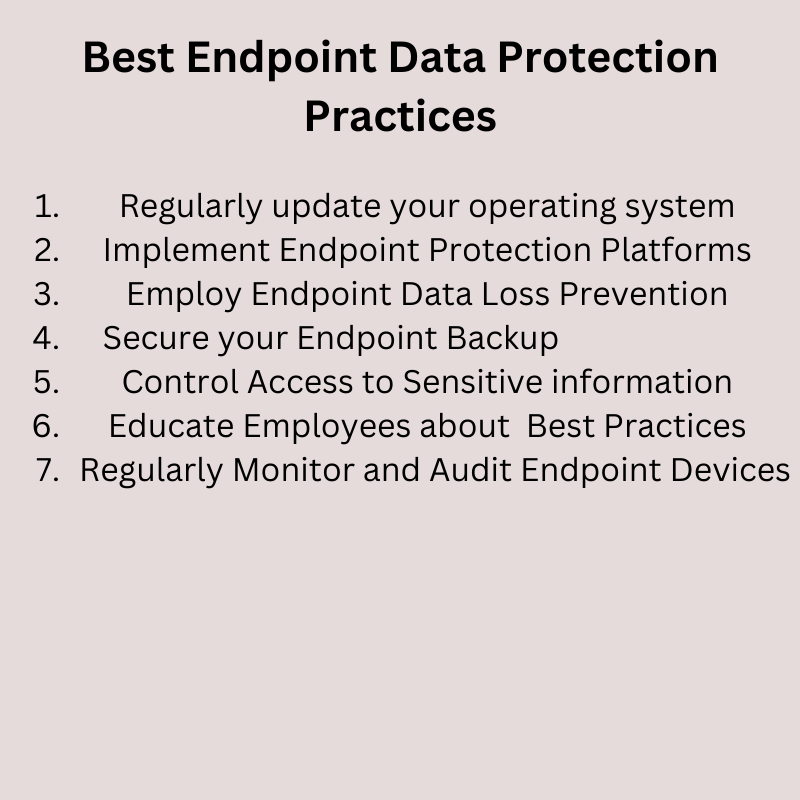
Security and compliance are not just checkboxes to be ticked off; they are crucial aspects of your business that can impact your reputation and bottom line. Investing in endpoint data protection is not just a smart move; it’s a necessary one. It is important that you have a plan including specific practices for endpoint security and data protection.
Frequently Asked Questions
- What is endpoint data loss prevention? Endpoint data loss prevention is a strategy that involves using tools and practices to prevent sensitive data from being lost, misused, or accessed by unauthorized users.
- What personal data does CyberArk process in order to provide Remote Access? CyberArk processes minimal personal data to provide Remote Access. This typically includes user credentials and activity logs.
- What data does Microsoft Defender for Endpoint store and how does it ensure privacy? Microsoft Defender for Endpoint collects security-related data, like threat and exploit information. It uses a variety of measures, including data anonymization and encryption, to ensure privacy.
- What are the main management capabilities available to the organization’s admin in Endpoint Protection? Endpoint Protection provides admins with capabilities like policy management, threat detection and response, and reporting and analytics.
- What features should be considered for optimum protection when selecting the best endpoint data protection solution? When selecting an endpoint data protection solution, consider features like threat detection and response, data loss prevention, device control, and integration with other security tools.

Experienced cybersecurity analyst, software engineer, patent attorney, worked with Linux, Windows, AWS, lots of security tools. Hope to help people do the right things and do the things right!