Introduction
In the digital age, securing your small business is more important than ever. With the rise of cyber threats, endpoint data security has become a frontline defense. This guide will walk you through the essentials of endpoint data security. Then it will show you how it can protect your business from potential threats.

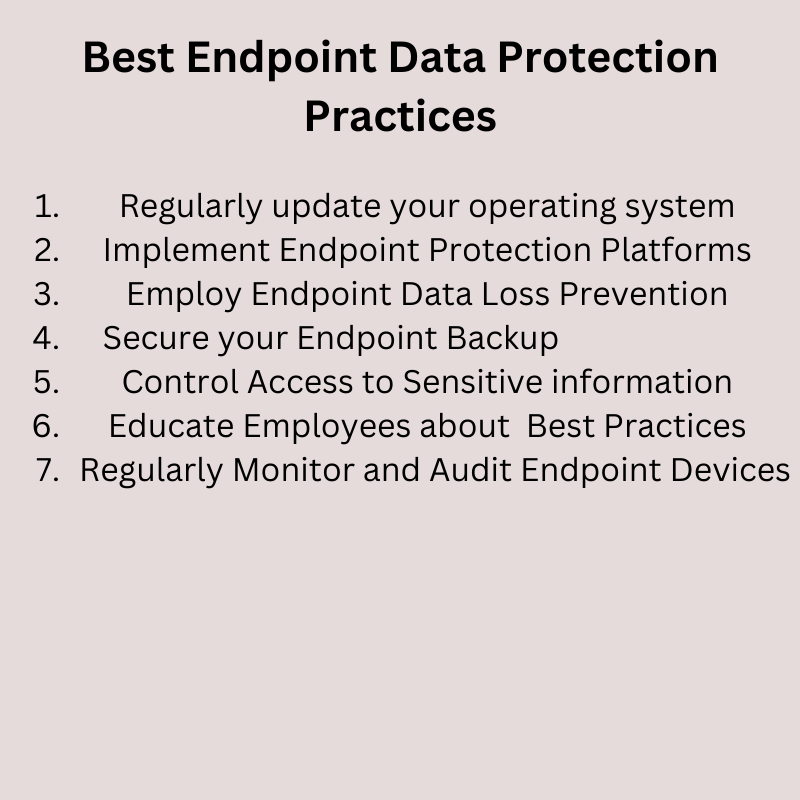
Understanding Endpoint Security
Endpoint security is about protecting the devices that connect to your network, such as desktops, laptops, and mobile devices. These devices, known as endpoints, can be vulnerable to cyber threats. By implementing endpoint security, you can safeguard your business data and maintain the integrity of your network.
The Role of Endpoint Protection Platforms (EPP)
Endpoint Protection Platforms (EPP) are software applications designed to secure endpoints. Central management oversees them, and they can detect, prevent, and respond to known and unknown threats. For example, an EPP might include antivirus software that scans your computers for harmful files. Using an EPP ensures protection for all endpoints within your network perimeter, which reduces the risk of a data breach.
The Perimeter of Your Network: Managing Endpoints Within
The perimeter of your network is the boundary that separates your internal network from the outside world. By managing only the endpoints within this perimeter, you can enhance your network security and prevent unauthorized access. For instance, you might use a firewall. A firewall is a tool that monitors and controls incoming and outgoing network traffic based on predetermined security rules.

Connecting to the Corporate Network Safely with VPNs
When an endpoint device connects to the corporate network, it can potentially expose the network to cyber threats. Therefore, it’s crucial to implement security measures that ensure safe connections. One such measure is a Virtual Private Network (VPN).
A VPN encrypts internet connections. Thus, ensuring secure access to the corporate network from remote locations. This is particularly useful for remote workers who need to access company resources securely.

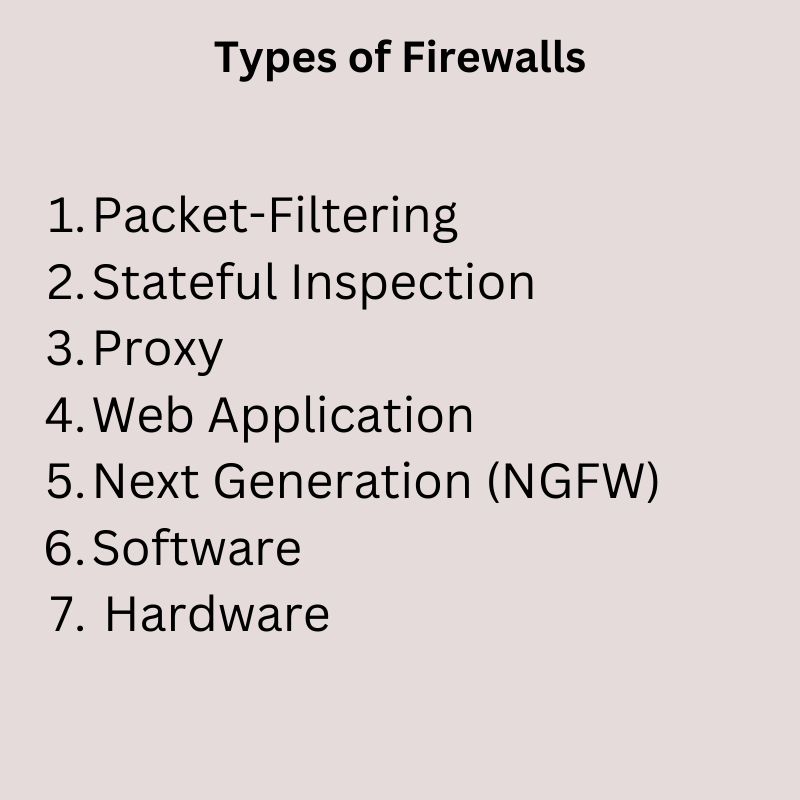
Securing Your Network with Firewalls
Firewalls are a crucial tool for network security. They monitor and control incoming and outgoing network traffic based on predetermined security rules, providing a barrier between your trusted internal network and untrusted external networks. There are several types of firewalls, each with its unique way of protecting your data.
By understanding these different types of firewalls and implementing the ones that best fit your business needs, you can enhance your network security and protect your valuable data from cyber threats.

Packet-Filtering Firewalls
These are the most basic type of firewall. They operate at the network level, inspecting packets (the basic units of data in a network). They block or allow these packets based on rules you set, such as IP addresses or port numbers. This is like a security guard checking IDs at the door, only allowing authorized personnel to enter.
Stateful Inspection Firewalls
These firewalls take security up a notch. They not only examine individual packets but also keep track of active connections. They can block or allow packets based on the state of these connections. It’s like a security guard who not only checks IDs but also keeps track of who is inside the building and what they’re doing.
Proxy Firewalls
Proxy firewalls act as intermediaries between two systems. They process requests on behalf of the other system, preventing direct connections. This can help hide your network details and provide additional security checks. It’s like having a personal assistant to screen your calls and handle your mail.
Web Application Firewalls (WAFs)
Web Application Firewalls protect your web applications by inspecting the content of traffic. They can detect and block common web-based threats such as cross-site scripting (XSS), SQL injection, and session hijacking. This is especially important if your business operates web applications that handle sensitive data. It’s like having a specialized security guard for your online store, protecting it from shoplifters and vandals.
Next-Generation Firewalls (NGFWs)
These are the advanced models of firewalls. They combine traditional firewall capabilities with other network device filtering functionalities, such as intrusion prevention systems (IPS) and application awareness. They can identify and block complex attacks. It’s like upgrading your security team with the latest equipment and training to handle any situation.
Software Firewalls
These firewalls are installed directly on a device and can provide personalized protection for that device. They control network traffic and protect against threats on a per-device basis. This is like having a personal bodyguard for each of your devices, ensuring they’re safe wherever they go.
Hardware Firewalls
These are standalone devices that sit between your network and the outside world. They provide high-level security and are often used in conjunction with software firewalls for layered protection. It’s like having a fortified wall around your business, keeping threats at bay.
Protecting Your Devices with Antivirus Software
Antivirus software is a fundamental tool for endpoint security. It scans for, detects, and removes malicious software and files, providing a basic level of security. Regularly updating your antivirus software ensures it can protect against the latest threats.

Managing Mobile Devices with MDM
With the rise of remote work and Bring Your Own Device (BYOD) policies, managing and securing mobile devices has become crucial. Mobile Device Management (MDM) solutions allow for the management and security of mobile devices used within a business. Thus ensuring they meet security standards and protecting them from threats.
Preventing Data Loss with DLP Tools
Data Loss Prevention (DLP) tools are essential for protecting sensitive data. They monitor and control data transfers, preventing sensitive data from leaving the corporate network. This is particularly important for businesses that handle customer data or other sensitive information.
Securing Data with Encryption Tools
Encryption tools encode data, making it unreadable to unauthorized users. Even if a breach occurs and someone steals data, they cannot read it without the correct decryption key. Encryption, a crucial tool, protects sensitive data, especially during transfer or storage.
Keeping Software Up-to-Date with Patch Management Tools
Patch Management Tools ensure that all software, including security software, is up to date. This reduces vulnerabilities that can be exploited by cyber threats. Regularly updating software is a simple but effective way to enhance your endpoint security.
Detecting Threats with Intrusion Detection Systems (IDS)
Intrusion Detection Systems (IDS) monitor network traffic for suspicious activity and issue alerts when such activity is detected. This helps to identify potential threats early, allowing for a quick response to prevent damage.
Conclusion
Endpoint data security is vital for the protection of your small business. At this point, you should understand these concepts. Hopefully you can implement the concepts discussed in this guide in your own system. Then you can safeguard your business from cyber threats and ensure the security of your data.
Frequently Asked Questions
- What is endpoint security example? Endpoint security can be an antivirus software installed on a company laptop that protects it from malware.
- What are the three main steps of endpoint security? The three main steps of endpoint security are: detection of threats, response to incidents, and continuous monitoring for new threats.
- What is the difference between EDR and endpoint security? Endpoint security is a general term for the methods used to secure network endpoints. EDR (Endpoint Detection and Response) is a specific technology used within endpoint security for monitoring endpoints and responding to threats.
- What is data endpoint security? Data endpoint security involves protecting the endpoints where data is received and transmitted, such as laptops, mobile devices, and servers, from cyber threats.
- How does endpoint security work? Endpoint security works by installing security software on the endpoints. This software monitors for and protects against threats, and can be managed centrally through a management console.

Experienced cybersecurity analyst, software engineer, patent attorney, worked with Linux, Windows, AWS, lots of security tools. Hope to help people do the right things and do the things right!