
Introduction
As we navigate through 2024, the digital realm is witnessing an unprecedented surge in cyber threats. According to a report by Cybersecurity Ventures, cybercrime damages are predicted to reach a staggering $10.5 trillion annually by 2025, up from $3 trillion in 2015. This alarming growth rate underscores the fact that cybercrime, if measured as a country, would rank as the world’s third-largest economy, trailing only the U.S. and China. Such statistics not only highlight the magnitude of the threat but also emphasize the importance of staying abreast with the latest cybersecurity tools and measures. In an era where data is the new gold, ensuring its security is paramount. As cyber threats evolve, so must our defenses. Leveraging the latest cybersecurity tools is no longer a luxury but a necessity for individuals, businesses, and nations alike.
The digital age has brought unprecedented opportunities for businesses, but it has also introduced a myriad of cybersecurity threats. Small businesses, often perceived as easy targets due to limited resources and security measures, are particularly vulnerable. A recent incident involving a suburban healthcare clinic highlights the gravity of the situation. The clinic was hit by a ransomware attack through an unsecured computer with outdated security software. The ransomware encrypted vital patient records and billing details. Faced with the potential loss of critical data, the clinic paid the ransom but still suffered data corruption and reputational damage. This incident underscores the importance of endpoint security, employee awareness, and regular data backups.
As cyber threats continue to evolve, it’s imperative for businesses, especially small ones, to stay informed and proactive in their cybersecurity measures. This article delves into the essential cybersecurity tools and practices that can help safeguard your business against such threats.
Goals of this article
The article underscores the financial implications of these threats, projecting significant growth in global cybercrime costs. To address these challenges, the post delves into common cybersecurity threats and stresses the need for proactive security measures. It provides a comprehensive overview of essential cybersecurity tools and best practices, with a particular focus on the significance of endpoint security.
The overarching purpose of this article is to advocate for a layered, holistic approach to cybersecurity, ensuring robust protection against the multifaceted threats of the digital world.
Some thought-provoking questions
- Adapting to Evolving Threats: How can businesses stay updated with the rapidly evolving landscape of cyber threats?
- Employee Training: What measures can be taken to ensure that employees are not the weakest link in the cybersecurity chain?
- Budget Constraints: How can small businesses prioritize which cybersecurity tools to invest in, given their budget limitations?
Useful Statistics About Endpoint Security and Threats
| Category | Statistic | Insight |
|---|---|---|
| Cybercrime Damage | – Damages predicted to be $8 trillion USD in 2023. | The importance of robust cybersecurity measures is underscored by the rapid growth in cybercrime damages. |
| – Costs to grow 15% annually, reaching $10.5 trillion USD by 2025. | ||
| – Ranks 8th among severe global risks over the next decade. | ||
| – Less than 25% of cybercrimes reported to law enforcement. | ||
| – Average data breach cost was $4.35 million USD in 2022. | ||
| Ransomware | – Damage costs to exceed $265 billion USD annually by 2031. | The significant rise in ransomware attacks highlights the need for a comprehensive ransomware response strategy. |
| – A business fell victim every 11 seconds in 2021. | ||
| Cryptocrime | – Will cost the world $30 billion USD in 2025. | |
| – Cryptocurrency fraud rose from $907 million USD in 2021 to $2.57 billion USD in 2022. |
Understanding the Digital Threat Landscape
Cyber threats are evolving. Gone are the days when a lone hacker would try to gain unauthorized access for fun. Today, cybercrimes are orchestrated by sophisticated criminal organizations and even state-sponsored groups. According to a report by Cybersecurity Ventures, global cybercrime costs could reach a whopping $10.5 trillion USD annually by 2025.
The digital realm is rife with threats that evolve continuously, posing significant challenges to businesses of all sizes. Understanding these threats is the first step towards building a robust defense.
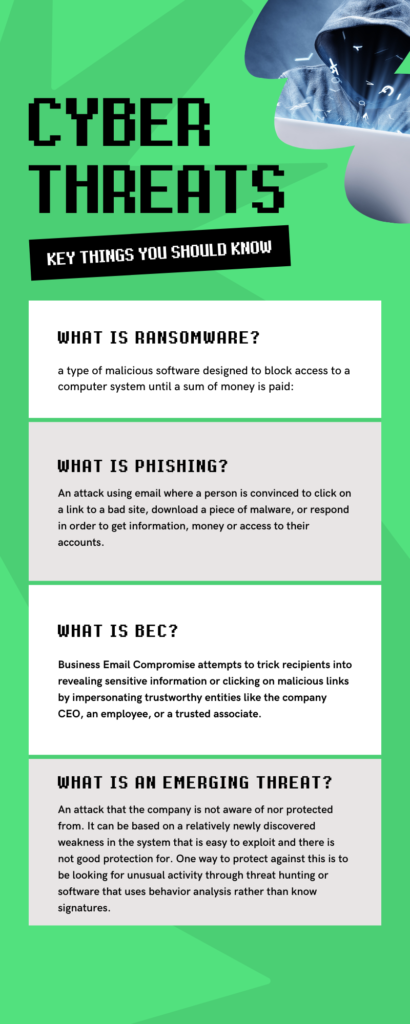
Ransomware
This malicious software encrypts an organization’s files, holding them hostage until a ransom is paid. Ransomware attacks have seen a dramatic surge, with incidents like the Colonial Pipeline attack causing widespread disruption. For small businesses, a ransomware attack can halt operations, leading to significant financial and reputational damage.
Phishing
A deceptive technique, phishing involves sending fraudulent messages that appear to come from trustworthy entities. The goal is to trick recipients into revealing sensitive information or clicking on malicious links. With 91% of cyber-attacks starting with a phishing email, it’s evident that this method is a preferred choice for cybercriminals. Small businesses are often targeted due to perceived weaker security measures, making them susceptible to data breaches and financial losses.
Business Email Compromise (BEC)
A more sophisticated form of phishing, BEC scams target businesses by compromising legitimate email accounts or impersonating executives. Attackers aim to deceive employees into transferring funds or sharing confidential data. The FBI has highlighted the significant financial impact of BEC scams, with losses exceeding billions. Small businesses, with potentially less stringent email security protocols, can be especially vulnerable.
Emerging Threats
As technology advances, so do cyber threats. Attackers now employ AI and machine learning to craft personalized scams, making them harder to detect. One such emerging threat is cryptojacking, where cybercriminals hijack victims’ computing power to mine cryptocurrency without their knowledge. For small businesses, this can lead to slowed operations and increased IT costs.
Understanding these threats is crucial for small businesses. By being aware of the risks and implementing appropriate security measures, they can safeguard their operations, data, and reputation in the digital landscape.
So, Why Endpoint Security?

Endpoints, like laptops, desktops, and mobile devices, are often the primary targets for cyberattacks. Ensuring these devices are secure is crucial. Top endpoint security solutions provide comprehensive protection for these endpoints.
The Bigger Picture: Layered Security
While endpoint security is essential, it’s just one piece of the puzzle. A holistic cybersecurity approach involves multiple layers, including:
- Email Security: Filtering malicious emails and attachments.
- Network & Perimeter Security: Monitoring network traffic to identify and block suspicious activities.
- Data Encryption: Encrypting sensitive business and customer data.
- Backup & Disaster Recovery: Regularly backing up critical data.
- Security Awareness Training: Educating employees on security best practices.
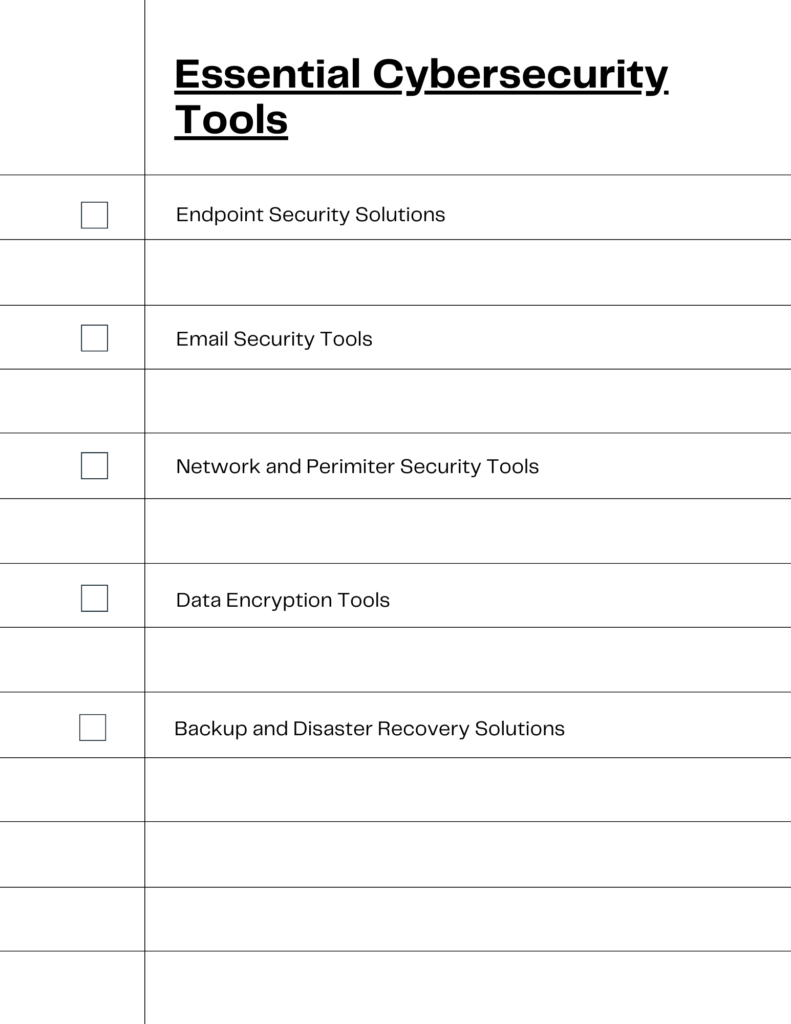
Essential Cybersecurity Tools for Small Businesses
The article also has a good discussion of the types of tools that one should have to protect small businesses.
- Endpoint Security Solutions: These tools focus on safeguarding individual devices that connect to a business network, such as laptops, desktops, and mobile devices. These solutions offer real-time monitoring, threat detection, and response mechanisms. For small businesses, endpoint security ensures that each device accessing the network is protected from potential cyber threats, reducing the risk of breaches.
- Email Security Tools: Given the prevalence of phishing and BEC scams, email security is paramount. These tools filter out malicious emails, attachments, and links, ensuring that only legitimate communications reach the recipients. They employ advanced algorithms to detect unusual patterns and block potential threats, safeguarding businesses from email-based attacks.
- Network & Perimeter Security: These tools monitor network traffic, identifying and blocking suspicious activities. They provide a protective barrier, ensuring that unauthorized entities cannot access the business network. For small businesses, this means continuous surveillance of all incoming and outgoing traffic, preventing potential intrusions.
- Data Encryption Tools: Data breaches can have severe consequences, especially if sensitive information is exposed. Encryption tools convert data into a code, preventing unauthorized access. Only those with the decryption key can access the original data. For small businesses, encrypting sensitive business and customer data is a proactive measure against potential breaches.
- Backup & Disaster Recovery Solutions: In the event of data loss due to cyberattacks, natural disasters, or human error, these tools ensure that businesses can quickly recover their data. Regular backups, cloud storage, and disaster recovery plans are essential for business continuity, minimizing downtime and financial losses.
By leveraging these tools, small businesses can build a comprehensive cybersecurity framework, ensuring robust protection against the multifaceted threats of the digital world.
Other Essential Cybersecurity Tools and Practices
In the vast landscape of cybersecurity, not all tools and practices are universally applicable. Different businesses have unique needs based on their industry, size, and the nature of their operations. It’s essential to recognize that while some cybersecurity measures are fundamental and should be adopted by all businesses, others might be more relevant to specific sectors or scenarios. The following breakdown categorizes essential cybersecurity tools and practices based on their importance and relevance to various types of businesses. This structured approach aims to guide businesses in identifying and prioritizing the cybersecurity measures most pertinent to their operations, ensuring a tailored and effective defense strategy.
For All Businesses
In the vast landscape of cybersecurity, not all tools and practices are universally applicable. Different businesses have unique needs based on their industry, size, and the nature of their operations. It’s essential to recognize that while some cybersecurity measures are fundamental and should be adopted by all businesses, others might be more relevant to specific sectors or scenarios. The following breakdown categorizes essential cybersecurity tools and practices based on their importance and relevance to various types of businesses. This structured approach aims to guide businesses in identifying and prioritizing the cybersecurity measures most pertinent to their operations, ensuring a tailored and effective defense strategy.
The Imperative Regular Software Updates
Regular software updates are not just about adding new features or fixing minor glitches. They are crucial for patching vulnerabilities that can be exploited by cybercriminals. When software is outdated, it becomes a prime target for malicious attacks, as these versions might have known security flaws.
For example, notable instance of the repercussions of not updating software is the 2017 WannaCry ransomware attack. This global cyberattack targeted computers running the Microsoft Windows operating system by encrypting data and demanding ransom payments in Bitcoin. The primary reason for the widespread impact of this attack was the exploitation of a vulnerability in older Windows versions. Microsoft had already released a security update to patch this vulnerability, but many organizations had not updated their systems. As a result, numerous businesses, including major hospitals in the UK, were severely affected, leading to significant financial losses and operational disruptions.
To avoid such catastrophic events, it’s imperative for businesses to prioritize and regularly implement software updates.
Secure Password Managers
Weak or reused passwords are a significant vulnerability. Password managers generate strong, unique passwords for each account and store them securely. They auto-fill passwords across devices and offer features like two-factor authentication, biometric login, and zero-knowledge encryption, ensuring that credentials remain protected.
Two-Factor Authentication (2FA)
2FA or multi-factor authentication adds an extra layer of security beyond just passwords. It requires users to verify their identity using a second factor, such as SMS codes, authenticator apps, or biometrics. Implementing 2FA on critical accounts like email and banking provides a robust defense against unauthorized access.
For E-Commerce and Online Retailers
In the digital age, e-commerce platforms and online retailers have revolutionized the way we shop. However, with this convenience comes a heightened risk. These digital storefronts are treasure troves of sensitive customer data, from personal details to payment information. As such, they are prime targets for cybercriminals. For e-commerce businesses, ensuring robust cybersecurity is not just about protecting company assets—it’s about preserving customer trust and maintaining brand reputation. In this section, we delve into the specific tools and practices that are paramount for e-commerce and online retailers to fortify their digital defenses.
SSL Certificates: Ensuring Secure Transactions and Building Trust
What are SSL Certificates?
SSL (Secure Socket Layer) certificates are digital certificates that authenticate the identity of a website and encrypt information sent to the server using SSL technology. When a website has an SSL certificate, it uses the HTTPS protocol instead of HTTP, indicating a secure connection. Visitors can identify secure sites by the padlock icon in the address bar.
Risks of Not Having or Updating SSL Certificates
- Data Breaches: Without an SSL certificate, data transferred between the user’s browser and the website is unencrypted. This makes it easier for cybercriminals to intercept and steal sensitive information, such as credit card details or login credentials.
- Loss of Customer Trust: Modern browsers warn users when they attempt to visit a website that doesn’t use SSL, often displaying a “Not Secure” warning. This can deter potential customers, leading to lost sales.
- Lower Search Engine Rankings: Search engines, like Google, prioritize secure websites in their rankings. Not having an SSL certificate can negatively impact a website’s SEO.
Suggestions for SSL Certificate Management
- Acquisition: If you don’t already have an SSL certificate, acquire one from a reputable Certificate Authority (CA). There are various types of SSL certificates, such as Domain Validation (DV), Organization Validation (OV), and Extended Validation (EV). Choose the one that best fits your business needs.
- Regular Renewal: SSL certificates have an expiration date. Ensure you renew your certificate before it expires to avoid website downtime and potential security risks.
- Implement HSTS: After setting up SSL, consider implementing HTTP Strict Transport Security (HSTS). This security measure ensures that browsers only connect to your server using a secure HTTPS connection.
- Regularly Monitor for Vulnerabilities: Stay updated with potential vulnerabilities related to SSL/TLS and ensure that your server configuration is always secure.
By ensuring that your e-commerce platform or online store has a valid and updated SSL certificate, you not only protect sensitive data but also build trust with your customers, assuring them that their information is safe with you.
Payment Security: Upholding Trust and Meeting Industry Standards
Understanding Payment Security: Payment security refers to the measures and protocols implemented to ensure that financial transactions conducted on a website are secure and free from threats. This encompasses everything from the encryption of credit card details to the secure processing of transactions.
Consequences of Lax Payment Security:
- Loss of Customer Trust: If customers feel that their financial information is at risk, they will likely abandon their carts and may never return. A single security breach can lead to long-term reputational damage.
- Penalties from Credit Card Companies: Credit card companies have set standards known as the Payment Card Industry Data Security Standard (PCI DSS). If businesses fail to comply with these standards, they can face hefty fines. Moreover, repeated non-compliance or breaches can lead to a business being barred from accepting credit card payments altogether.
- Financial Repercussions: Apart from fines, businesses may also be held liable for any fraudulent transactions, leading to direct financial losses.
Recommendations for Ensuring Payment Security:
- PCI DSS Compliance: Ensure that your business adheres to the PCI DSS standards. This not only helps in avoiding penalties but also ensures that you’re following best practices for payment security.
- Use Trusted Payment Gateways: Opt for reputable payment gateways like Stripe, PayPal, or Square. These platforms have robust security measures in place and are widely trusted by consumers.
- Never Store Customer Payment Information: Unless absolutely necessary and with proper security measures, avoid storing customer credit card details on your servers. If you must store them, ensure they are encrypted and tokenized.
- Regular Security Audits: Conduct regular security audits to identify and rectify potential vulnerabilities in your payment processing system.
By prioritizing payment security, businesses not only uphold the trust of their customers but also ensure that they remain in good standing with credit card companies. In the e-commerce realm, where transactions are the lifeblood of business, ensuring secure payments is non-negotiable.
DDoS Protection: Shielding Your Digital Storefront from Disruption
Understanding DDoS Attacks
Distributed Denial of Service (DDoS) attacks involve overwhelming a website or online service with excessive traffic, rendering it slow or completely inaccessible. These attacks can be motivated by various reasons, from competitive business tactics to mere vandalism. For e-commerce platforms, even a short period of downtime can result in significant revenue loss and damage to brand reputation.
The Impact of DDoS Attacks
- Business Disruption: A successful DDoS attack can bring your online operations to a halt, preventing customers from making purchases and accessing services.
- Loss of Revenue: Every minute your website is down, you’re potentially losing sales. For high-traffic e-commerce sites, this can translate to substantial financial losses.
- Erosion of Trust: Repeated website outages can erode customer trust, making them hesitant to return or recommend your platform to others.
Leveraging Tools like Cloudflare for Protection
Cloudflare, among other DDoS protection services, offers a robust solution to guard against these attacks. Here’s how tools like Cloudflare can be instrumental:
- Traffic Filtering: Cloudflare and similar platforms can differentiate between legitimate traffic and malicious requests, allowing genuine users to access your site while blocking malicious entities.
- Global Content Delivery Network (CDN): By distributing web content across a global network of servers, Cloudflare ensures that even if one server is under attack, users can still access your site from another server.
- Real-time Monitoring: Get insights into your website’s traffic, allowing you to detect and respond to threats in real-time.
- Ease of Setup: Implementing Cloudflare is straightforward, requiring minimal changes to your existing website infrastructure.
Guarding the Fortresses of Sensitive Data: Healthcare and Finance
In the realm of data sensitivity, sectors like healthcare and finance stand out prominently. These industries handle some of the most personal and confidential information, from medical histories to financial transactions. A breach in these sectors doesn’t just mean financial loss; it can have profound implications on individuals’ lives, privacy, and well-being. The stakes are incredibly high, and the responsibility on businesses in these sectors is immense. In this section, we delve into the specialized cybersecurity measures that businesses handling sensitive data must prioritize to ensure the utmost protection of their digital assets and the trust of their clientele.
Data Encryption Tools: The Dual Shield for Sensitive Information
Understanding Data Encryption
Data encryption transforms readable data (plaintext) into an encoded version (ciphertext) that can only be decoded with a specific key. It’s a fundamental tool in the cybersecurity arsenal, especially for businesses in sectors like healthcare and finance that handle highly sensitive information.
The Dual Necessity: Encryption in Transit and at Rest
- Encryption in Transit: As data travels over the internet, be it through emails, online transactions, or data transfers, it’s susceptible to interception by malicious entities. Encrypting data in transit ensures that even if data is intercepted, it remains unreadable without the decryption key. Tools like SSL/TLS certificates, which we discussed earlier, play a crucial role in encrypting data in transit.
- Encryption at Rest: While it’s vital to protect data as it moves, it’s equally crucial to secure it where it’s stored, be it on servers, databases, or cloud storage. Encrypting data at rest ensures that unauthorized individuals or entities can’t access the stored data, even if they breach the storage infrastructure.
Why is Data Encryption Essential?
- Protection Against Breaches: Even if cybercriminals manage to infiltrate a system, encrypted data remains unintelligible without the decryption key.
- Regulatory Compliance: Many industries have regulations that mandate the encryption of certain types of data. Non-compliance can result in hefty fines and legal repercussions.
- Building Trust: Customers and clients are more likely to trust businesses that prioritize the security of their data. Encryption showcases a company’s commitment to data protection.
In an era where data breaches are increasingly common, encryption acts as a last line of defense, ensuring that sensitive information remains secure even in worst-case scenarios. For businesses handling sensitive data, implementing robust encryption tools isn’t just a recommendation; it’s a necessity.
Intrusion Detection Systems: The Digital Watchtower
Understanding Intrusion Detection Systems (IDS)
Intrusion Detection Systems, often abbreviated as IDS, act as vigilant sentinels for digital networks. They continuously monitor network traffic, analyzing it for signs of malicious activities or policy violations. Think of IDS as a digital watchtower, always on the lookout for potential threats trying to breach the castle walls.
The Core Function: Monitoring Network Traffic for Suspicious Activities
- Signature-Based Detection: This method involves comparing network traffic against a database of known attack patterns or signatures. If a match is found, an alert is generated.
- Anomaly-Based Detection: IDS systems establish a baseline of “normal” network behavior. Any deviation from this baseline, which might indicate a potential threat, is considered an anomaly and triggers an alert.
Why are Intrusion Detection Systems Essential?
- Proactive Threat Management: Instead of reacting to breaches after they occur, IDS allows businesses to detect and address threats in real-time, often before any damage is done.
- Comprehensive Visibility: IDS provides a holistic view of network activities, helping businesses identify potential vulnerabilities and areas of improvement in their security infrastructure.
- Regulatory Compliance: For sectors like finance and healthcare, having an IDS might be a regulatory requirement, ensuring that sensitive data remains protected against potential breaches.
- Building and Maintaining Trust: Knowing that a business has systems in place to detect and counter threats in real-time can bolster client and customer trust.
In the ever-evolving landscape of cyber threats, having an Intrusion Detection System is akin to having a dedicated security team that never sleeps. It ensures that businesses are always a step ahead of potential attackers, safeguarding their digital assets and maintaining the sanctity of their operations.
Regular Data Backups: Your Digital Safety Net
Understanding the Importance of Data Backups
In the digital age, data is often referred to as the new gold. It’s the lifeblood of businesses, containing everything from customer information to crucial business strategies. But just as gold needs to be securely stored and insured, so does data. Regular data backups ensure that even in the face of unexpected events or cyberattacks, your business can recover and continue operations with minimal disruption.
The Dual Mandate: Regular Backups and Secure Storage
- Frequency is Key: Data should be backed up regularly, with the frequency depending on the nature of the business. For some, daily backups might be necessary, while for others, weekly or bi-weekly backups might suffice.
- Diverse Storage Locations: Storing backup data in multiple locations, both on-site and off-site, ensures that even if one backup is compromised or destroyed, others remain accessible. Cloud storage solutions, external hard drives, and secure data centers are popular choices.
Why Regular Data Backups are Essential
- Mitigating Ransomware Attacks: One of the most prominent threats businesses face today is ransomware, where attackers encrypt data and demand a ransom for its release. With regular backups, businesses can restore their data without paying the ransom. For instance, the city of Atlanta, when hit by a ransomware attack in 2018, relied on backups to restore many of its systems, mitigating the impact of the attack.
- Recovery from Accidental Deletions: Human errors, such as accidental data deletions, can be as damaging as cyberattacks. Backups ensure that such mistakes don’t result in permanent data loss.
- Business Continuity: Natural disasters, hardware failures, or other unforeseen events can disrupt business operations. Having data backups ensures that businesses can quickly resume operations in such scenarios.
Examples of Effective Backup Strategies:
- 3-2-1 Backup Rule: This strategy involves having three total copies of your data, two of which are on different mediums or platforms, and one of which is stored off-site.
- Incremental Backups: Instead of backing up all data every time, only changes made since the last backup are stored. This saves storage space and reduces backup time.
In conclusion, regular data backups are not just a best practice but a necessity in today’s digital landscape. They act as a safety net, ensuring that come what may, your business’s digital assets remain protected and accessible.
For Remote Work and Distributed Teams
The modern workplace is no longer confined to the four walls of an office. With the rise of remote work and distributed teams, businesses are operating across cities, countries, and even continents. While this new mode of work offers unparalleled flexibility and access to global talent, it also brings forth unique cybersecurity challenges. From unsecured home networks to the risks of public Wi-Fi, the digital workspace is vast and varied. In this section, we explore the essential cybersecurity measures that businesses must implement to ensure that their remote workforce operates securely, no matter where they are.
Virtual Private Networks (VPNs): The Secure Tunnel for Remote Connections
Understanding VPNs
A Virtual Private Network, commonly known as a VPN, is a technology that creates a secure and encrypted connection over a less secure network, such as the internet. It acts as a tunnel, ensuring that data transmitted between a remote user and the company’s network remains private and protected from potential eavesdroppers.
The Core Function: Securing Remote Connections
- End-to-End Encryption: VPNs encrypt data at the sending end and decrypt it at the receiving end. This ensures that even if data is intercepted during transmission, it remains unreadable without the decryption key.
- Masking IP Addresses: VPNs mask the user’s IP address, making it difficult for hackers to pinpoint the location or identity of the user.
- Secure Access to Company Resources: Remote employees can securely access company files, databases, and other resources as if they were physically present in the office.
Why are VPNs Essential for Remote Work?
- Protection on Unsecured Networks: Remote workers often connect to public Wi-Fi networks in cafes, airports, or hotels. These networks are notorious for being less secure. VPNs ensure that data remains protected even on such networks.
- Regulatory and Compliance Needs: For industries that handle sensitive data, using a VPN might be a regulatory requirement to ensure data protection.
- Preventing Unauthorized Access: VPNs often come with multi-factor authentication, adding an additional layer of security. This ensures that only authorized personnel can access the company’s network.
In the era of remote work, VPNs are not just a tool but a necessity. They act as a secure bridge between remote employees and the company’s resources, ensuring seamless and safe connectivity. As businesses continue to embrace the flexibility of remote work, the importance of VPNs in the cybersecurity toolkit cannot be overstated.
Endpoint Security Solutions: Guarding Every Digital Doorway
Understanding Endpoint Security
Endpoint security refers to the protection of internet-connected devices, such as laptops, smartphones, and tablets, from potential cyber threats. These devices, often referred to as “endpoints,” serve as entry points to the company network. As the number of devices connecting to corporate networks increases, especially with the prevalence of remote work, ensuring the security of each endpoint becomes paramount.
The Core Function: Securing Every Device Connecting to the Network
- Real-time Monitoring: Endpoint security solutions continuously monitor devices for signs of malicious activities, ensuring threats are detected and addressed in real-time.
- Regular Device Scans: These solutions routinely scan devices for vulnerabilities, outdated software, or malicious applications, ensuring they remain compliant with security policies.
- Remote Access Control: In case a device is lost or compromised, endpoint security allows IT teams to remotely lock the device or wipe sensitive data, safeguarding company information.
Why are Endpoint Security Solutions Essential?
- Diverse Threat Landscape: With a variety of devices connecting to the network, each with its own operating system and software, the potential vulnerabilities multiply. Endpoint security ensures a standardized level of protection across all devices.
- Protection Against Phishing and Malware: These solutions can detect and block phishing attempts and malware installations, two of the most common threats faced by remote workers.
- Regulatory Compliance: For sectors with stringent data protection regulations, ensuring endpoint security might be a mandatory requirement.
In a world where work is no longer confined to the office, and devices of all kinds connect to company networks from various locations, endpoint security stands as the first line of defense. It ensures that every digital doorway into the company’s network is guarded, allowing businesses to operate with confidence in the digital realm.
Collaborative Tool Security: Safeguarding Team Interactions in the Digital Space
Understanding Collaborative Tool Security
In today’s interconnected work environment, teams rely heavily on collaborative tools for communication, project management, and document sharing. Whether it’s video conferencing platforms, chat applications, or cloud-based document editors, these tools have become the backbone of modern teamwork. However, their widespread use also makes them attractive targets for cyber threats, necessitating robust security measures.
The Core Function: Ensuring Secure Communication and Collaboration
- End-to-End Encryption: Many collaborative tools now offer end-to-end encryption, ensuring that communications, whether text chats or video calls, remain private and are only accessible to the intended recipients.
- Regular Software Updates: Collaborative tool providers frequently release updates to patch vulnerabilities and enhance security features. Regularly updating these tools is crucial to benefit from the latest security enhancements.
- Access Controls: Implementing strict access controls ensures that only authorized personnel can access shared documents or join collaborative sessions. Features like two-factor authentication add an extra layer of security.
Why is Collaborative Tool Security Essential?
- Protection of Sensitive Information: Collaborative sessions often involve discussions on company strategies, financial data, or other sensitive information. Ensuring the security of these tools protects this valuable data from potential eavesdroppers.
- Mitigating Data Breaches: Secure collaborative platforms reduce the risk of data breaches, where unauthorized individuals gain access to shared documents or communication logs.
- Building Trust with Stakeholders: When clients, partners, or employees know that their communications are secure, it fosters trust and encourages open collaboration.
In an era where remote collaboration is the norm, ensuring the security of the tools we use is paramount. It’s not just about protecting data; it’s about ensuring that teams can collaborate freely, innovate, and drive business growth without the looming shadow of cyber threats. Secure collaborative tools are the foundation of a resilient and forward-thinking organization.
For Brick-and-Mortar Businesses
While traditional brick and mortar businesses may not operate predominantly in the digital realm, the integration of technology into their operations is undeniable. From point-of-sale systems and inventory management to customer relationship platforms, even the most conventional businesses have a digital footprint. This section delves into the unique cybersecurity challenges faced by physical storefronts and offers tailored solutions to ensure that while they serve customers face-to-face, their digital back-end remains fortified against potential threats.
Physical Security: Fortifying the First Line of Defense
Understanding the Importance of Physical Security
While the digital realm often takes center stage in discussions about security, the physical security of a business premises remains a cornerstone of comprehensive protection. Brick and mortar establishments, with tangible assets and on-site personnel, require measures to deter, detect, and respond to real-world threats.
Key Components of Physical Security
- Security Cameras: These act as both a deterrent and a means of evidence collection. Strategically placed cameras monitor key areas of the business, capturing any unauthorized activities. Modern security cameras also come with features like motion detection and night vision, enhancing their effectiveness.
- Access Control Systems: These systems regulate who can enter the business premises or specific areas within it. Whether it’s through key cards, biometric scans, or pin codes, access control ensures that only authorized individuals can gain entry.
- Security Personnel: Trained security guards can respond to immediate threats, provide surveillance, and offer a visible deterrent to potential intruders.
Why is Physical Security Essential for Brick and Mortar Businesses?
- Protection of Assets: Physical assets, whether it’s inventory, equipment, or cash reserves, are vulnerable to theft or damage. Security measures reduce this risk.
- Safety of Personnel: Employees and customers should feel safe within the business premises. Physical security measures ensure their protection against potential threats.
- Deterrence: The mere presence of security cameras or access control systems can deter potential criminals, reducing the risk of break-ins or vandalism.
- Business Continuity: In the event of a security breach, having recorded evidence can aid in investigations and insurance claims, ensuring the business can recover and continue operations.
In conclusion, while the world increasingly shifts online, the importance of physical security remains undiminished. For brick and mortar businesses, it’s not just about protecting assets; it’s about creating a safe environment where business can thrive, employees can work without fear, and customers can shop with confidence.
Point of Sale (PoS) Security: Safeguarding the Heartbeat of Retail Transactions
Understanding the Importance of PoS Security
The Point of Sale (PoS) system is where the majority of retail transactions occur, making it a critical component of brick and mortar businesses. As these systems process sensitive financial data, such as credit card information, they become prime targets for cybercriminals. Ensuring the security of PoS systems is not just about protecting financial transactions; it’s about maintaining customer trust and safeguarding the reputation of the business.
Key Aspects of PoS Security
- Regular Software Updates: PoS software providers frequently release updates to patch vulnerabilities and enhance security features. It’s imperative to keep the system updated to benefit from the latest protections.
- End-to-End Encryption: Encrypting data at the point of capture ensures that it remains secure as it travels through the transaction process. Even if intercepted, encrypted data remains unreadable without the decryption key.
- Multi-factor Authentication: Implementing multi-factor authentication for accessing the PoS system adds an additional layer of security, ensuring that only authorized personnel can process transactions.
- Network Segmentation: Keeping the PoS system on a separate network from other business operations minimizes the risk of cross-contamination in the event of a breach.
Why is PoS Security Essential?
- Protection of Financial Data: With the vast amount of credit card and transaction data processed, PoS systems are treasure troves for cybercriminals. Ensuring their security is paramount to protect both the business and its customers.
- Maintaining Customer Trust: Customers trust businesses with their financial information. A breach can erode this trust, leading to loss of clientele and potential legal repercussions.
- Regulatory Compliance: Many regions have strict regulations regarding the protection of financial data. Ensuring PoS security is often a regulatory requirement, with non-compliance leading to hefty fines.
In conclusion, the PoS system is more than just a transactional tool; it’s a gateway that bridges the trust between a business and its customers. In an age where data breaches are increasingly common, ensuring the security of PoS systems is a non-negotiable aspect of running a successful brick and mortar establishment.
Employee Training and Awareness
Human error, like clicking on phishing links or using weak passwords, often leads to breaches. Regular, interactive security awareness training educates employees on secure practices. Training should cover malware prevention, strong passwords, recognizing social engineering tactics, safe web use, and handling sensitive data responsibly.
Incident Response Preparedness
A detailed incident response plan is crucial. It should outline steps for containment, eradication, recovery, and communication during a cyber incident. Regular drills and retaining log data for post-incident forensic investigations are also essential.
Regular Risk Assessments
Proactively assess risks across the organization’s people, processes, data, and technology. Regular audits, penetration testing, and threat modeling help identify vulnerabilities and guide action steps to mitigate potential threats.
Layered Security Approach
With the complexity of modern cyber threats, a single security tool or control is insufficient. A layered approach, known as defense in depth, combines multiple overlapping security tools. This holistic protection ensures that even if one security layer is compromised, additional controls still provide protection.
By integrating these tools and practices into their cybersecurity strategy, businesses can ensure a comprehensive defense against a wide range of threats, safeguarding their assets and reputation in the digital landscape.
Conclusion
In the digital age, cybersecurity is not a destination but a continuous journey. As technology advances, so do the tactics and techniques of cybercriminals. For businesses, whether brick and mortar or purely online, the challenge is to stay one step ahead, constantly adapting and evolving their security measures.
The tools and practices highlighted throughout this guide are foundational, but they are just the beginning. Cybersecurity requires ongoing vigilance, regular assessments, and a proactive approach. It’s about fostering a culture where security becomes second nature, where employees are educated about potential threats, and where systems are routinely updated and fortified.
Moreover, as businesses grow and expand, their cybersecurity needs will change. New vulnerabilities may emerge, and fresh challenges will arise. It’s crucial for businesses to recognize that cybersecurity is not a one-time investment but an ongoing commitment.
In the end, the goal is not just to protect data or assets but to safeguard the very essence of a business – its reputation, its relationship with customers, and its position in the market. In a world where data breaches and cyberattacks are becoming commonplace, a robust and adaptive cybersecurity strategy is the best defense and the key to enduring success.
Cybersecurity is not a one-time task; it’s an ongoing process. And while tools and technologies are essential, awareness and education are equally crucial. So, take a moment to dive deeper into the world of cybersecurity.
Share your thoughts in the comments!

Experienced cybersecurity analyst, software engineer, patent attorney, worked with Linux, Windows, AWS, lots of security tools. Hope to help people do the right things and do the things right!


